Multi-factor Authentication (MFA)
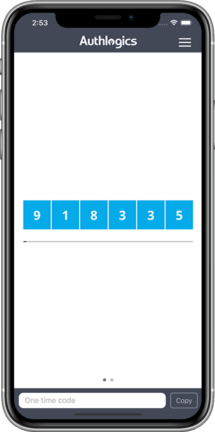
A One Time PIN (OTP) is typically a short sequence of numbers, similar to a PIN, however you don't have to remember anything and the numbers change every time you use it.
(MFA) is quite simple, and organizations are focusing more than ever on creating a smooth user experience for Authentication. In fact, you probably already use it in some form. For example, you’ve used (MFA) if you’ve:
- Swiped your bank card at the ATM and then entered your PIN (Personal ID Number).
- Logged into a website that sent a numeric code to your phone, which you then entered to gain access to your account.
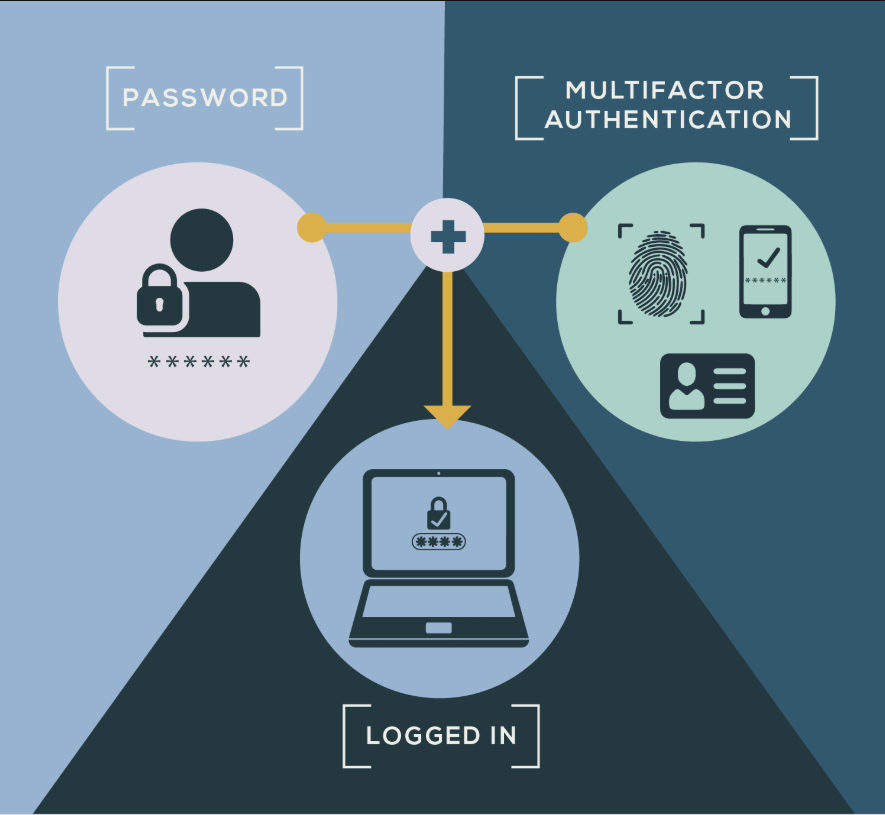
(MFA), sometimes referred to as two-factor authentication or 2FA, is a security enhancement that allows you to present two pieces of evidence – your credentials – when logging in to an account. Your credentials fall into any of these three categories: something you know (like a password or PIN), something you have (like a smart card), or something you are (like your fingerprint). Your credentials must come from two different categories to enhance security – so entering two different passwords would not be considered multi-factor.
In KFUPM, MFA will be implemented as 2FA using Authlogics’ PINpass and PINgrid pins.
Google Authenticator will be replaced by Authlogics (PINgrid / PINpass) technology.
PINpass One Time Pin (OTP), also called onetime code, generated on a separate device without the cost and complexity of traditional hardware token solutions.
The PINpass OTP can be provided via the free Authlogics Authenticator mobile application. The PINpass OTP is used as MFA for KFUPM services such as :
https://mail.kfupm.edu.sa, https://password.kfupm.edu.sa, https://vpn.kfupm.edu.sa
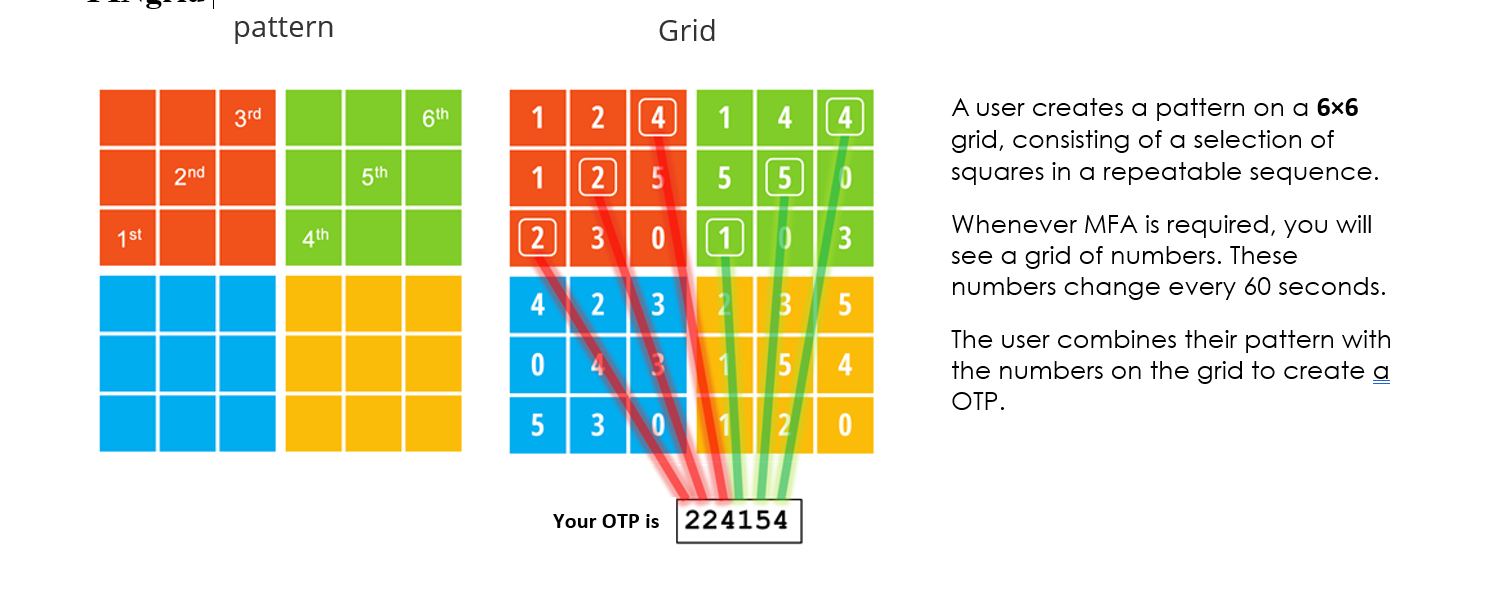
PINgrid is a simple-to-use but solid authentication technology which uses a secret user-generated shape or pattern to generate a One-Time Pin (OTP). Your pattern remains secret but the OTP it generates changes every time you logon.
Both can be used interchangeably. Some services like https://mail.kfupm.edu.sa are easier with PINgrid as the grid pattern is available on the web page itself and the secondary device to get the OTP is not needed.
- You should receive an enrollment E-mail containing the login details.
- Visit MFA Self-Service portal i.e. https://mfa.kfupm.edu.sa to manage your account and to add your mobile device.
- Enter your KFUPM credentials for logging on for the first time.
- Download Authlogics Authenticator application on any supported device and link it with your account. The application is available on Apple Store, Android Store, Microsoft Store and Amazon Store.

- Copy Device ID from the application’s settings
- Go back to Devices in MFA portal and add the Device using ID.
- Congrats, you have setup (MFA) once the application is linked.
- For more detailed steps, please refer to the below documents:
For detailed step by step guide, please follow “Multi-factor Authentication (MFA) – User Guide”
MFA setup is required in following conditions:
- Once it’s enabled for you for the first time.
- Whenever you change your device.
- Whenever you want to add a new additional device for MFA.
- Whenever you re-install the Authlogics Authenticator application in your mobile device.
Initially, it will be used to access web email i.e. https://mail.kfupm.edu.sa, https://password.kfupm.edu.sa, https://vpn.kfupm.edu.sa. Subsequently, it will be applied to all other KFUPM services. The ICTC will keep on informing KFUPM community as and when services will be enabled for (MFA).
Yes, it is mandatory as it adds another layer of protection from the kinds of damaging attacks that cost university its reputation as well as hamper business communication.
There are multiple ways you can add your device:
- How to install Android app and add Android device
- How to install iOS app and add IOS device
- How to install Windows Store app and add Windows device
For detailed step by step guide, please follow “ Multi-factor Authentication (MFA) – User Guide "
Authlogics Authenticator application is available for: Android platform, iOS platform, and Windows platform.
Yes, the user can enroll multiple devices for (MFA).
Every time you need to login in to an MFA enabled service, OTP authentication is required.
You can use a secondary device if it is added in your MFA Self-Service portal, to logon to MFA or any other MFA enabled service e.g. mail.kfupm.edu.sa.
In case, you lost your only device that was added in your MFA Self-Service portal, then,
call helpdesk at 3111. Helpdesk personnel will allow you to use your domain credentials temporarily so that you can on-board a new device in the self-service portal to do so,
- Go to https://mfa.kfupm.edu.sa
- Use domain credentials KFUPM <username>/<password> to sign-in to MFA Self-Service portal.
- Add device as mentioned in the previous question <How to add user devices for (MFA)?>
- Go to https://mfa.kfupm.edu.sa
- Use domain credentials KFUPM <username>/<password> to sign-in to MFA Self-Service portal.
- Go to Devices in the left hand side menu.
- Select the device from the list and click remove.
Since the PINpass is a One-Time-Password (OTP), therefore it is usable only once, and it changes every 60 seconds.
At minimum, the pattern must exist in two colors.
Following are unaccepted patterns:
- All consecutive or connected boxes in a single row.
- All consecutive or connected boxes in a single column.
- All diagonal boxes.
- All six boxes are chosen from a single color.
Setup the Authlogics Authenticator application only on the devices that belong to you e.g. your mobile phone, your tablet, your desktop/laptop etc. The second factor is actually "something you have", so that only you can see your OTP. If you add someone else's device in your MFA Self-Service portal, you would end up revealing your OTP to that person and eventually compromise your authenticity.
(MFA) prevents an attacker from many attacks such as man-in-the-middle attack, sniffing attack, shoulder surfing attack, dictionary attack, session replay attack etc.
This is against security practices. We strictly advise not to add one device to more than one user account. If a device is added to more than one account, it would mean that those account holders or users share the same second-factor-passcode as in sharing the same password!
It’s a two-step process and there are two approaches for it.
Approach # 1:
1. Go to MFA Self-Service portal, delete the enrolled device's information
2. Next, uninstall the MFA application from mobile device.
Now, the user will be able to login to MFA Self-Service portal with his KFUPM AD credentials and then add the new device easily.add the new device easily.
Approach # 2:
1.Install Authlogics app in the new device and then add the new device in MFA Self-Service portal
2. Remove the old device from MFA Self-Service portal.
If you have already done this, then call 3111 and take help from support guys to add the new device ID in your MFA Self-Service portal. Note that every installation of Authlogics Authenticator generates a new device ID. As soon as you uninstalled the Authlogics application, your device got unlinked with your MFA profile thus making your device unusable for PIN passcode.
Following are the right steps if you want to uninstall and reinstall the Authlogics Authenticator application;
1. Logon to MFA Self-service Portal, https://mfa.kfupm.edu.sa
2. Go to Devices.
3. Select the already added device and remove it. Keep the portal signed in.
4. On your windows PC, uninstall and reinstall Authlogics Authenticator app.
5. Go back to MFA Self-Service portal.
6. If the session is already signed in, just add the device again. Get the Device ID (12-digit number) from the newly installed Authlogics app. (NOTE: Device ID changes with new installation). On the other hand, if session of MFA Self-Service portal is ended then write your username in username box and then click on "logon using Windows credentials". Add the device under Devices. Do not close the MFA Self-Service portal.
7. Open an incognito browser window and try sign-in to MFA Self-Service portal with the PIN generated by the newly installed Authlogics app. If it works, you are good to go with E-mail access too. You can now close all browsers and resume your work. If you are unable to sign-in to MFA Self-Service portal with the new PIN, then go back to already open MFA Self-Service portal and verify the device ID.